DLP CONFIGURATION WITH EXCHANGE AGENT
DLP CONFIGURATION WITH EXCHANGE AGENT
1.Windows Server with MS Exchange Installed
2.GW with DLP blade enabled
3.Exchange Agent
1.Enable DLP on the gateway and also enable user check client support with out which the end user will not get any user check messages. Also allow notification emails so that users using outlook can get notification mails.
Enabling self handling is also important since the user can login to the portal and either send the mail or discard it from the dlp portal gateway properties and dlp portal details are as below.
3.Once you have installed the the exchange agent on both exchange server as well as on dashboard you can initialize the sic between the gateway and the exchange agent.
5.Also for dlp to work optimum you need to edit a parameter under $DLPDIR/dlp/config/dlp.conf, you need to edit the consider_ip_address_in_smtp to yes refer to screen shot below.
Pre-requisites
1.Windows Server with MS Exchange Installed
2.GW with DLP blade enabled
3.Exchange Agent
Configuration
1.Enable DLP on the gateway and also enable user check client support with out which the end user will not get any user check messages. Also allow notification emails so that users using outlook can get notification mails.
Enabling self handling is also important since the user can login to the portal and either send the mail or discard it from the dlp portal gateway properties and dlp portal details are as below.
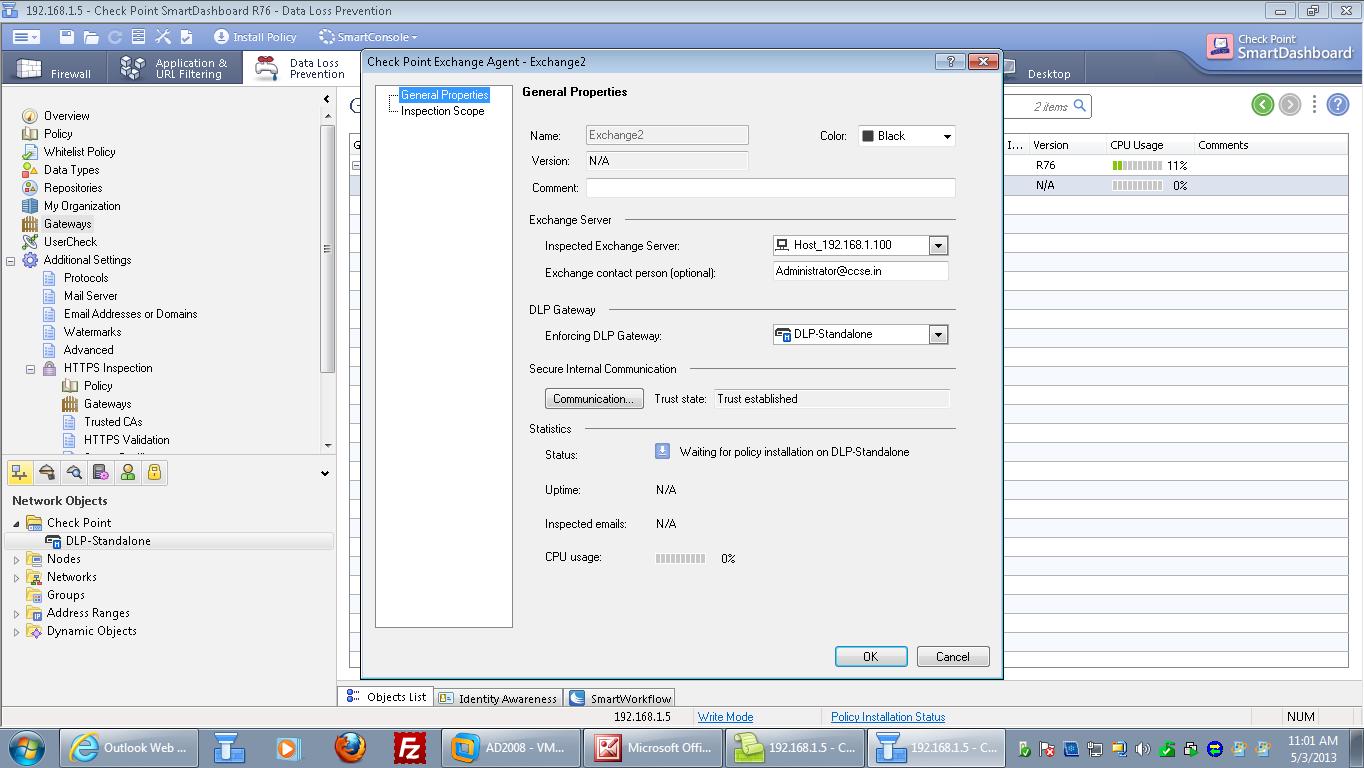
2.Once
you have installed the Exchange server on your windows server you can
install exchange agent on the exchange server. And configure the same in
smart dashboard under dlp tab > Gateways refer to screen shot below.
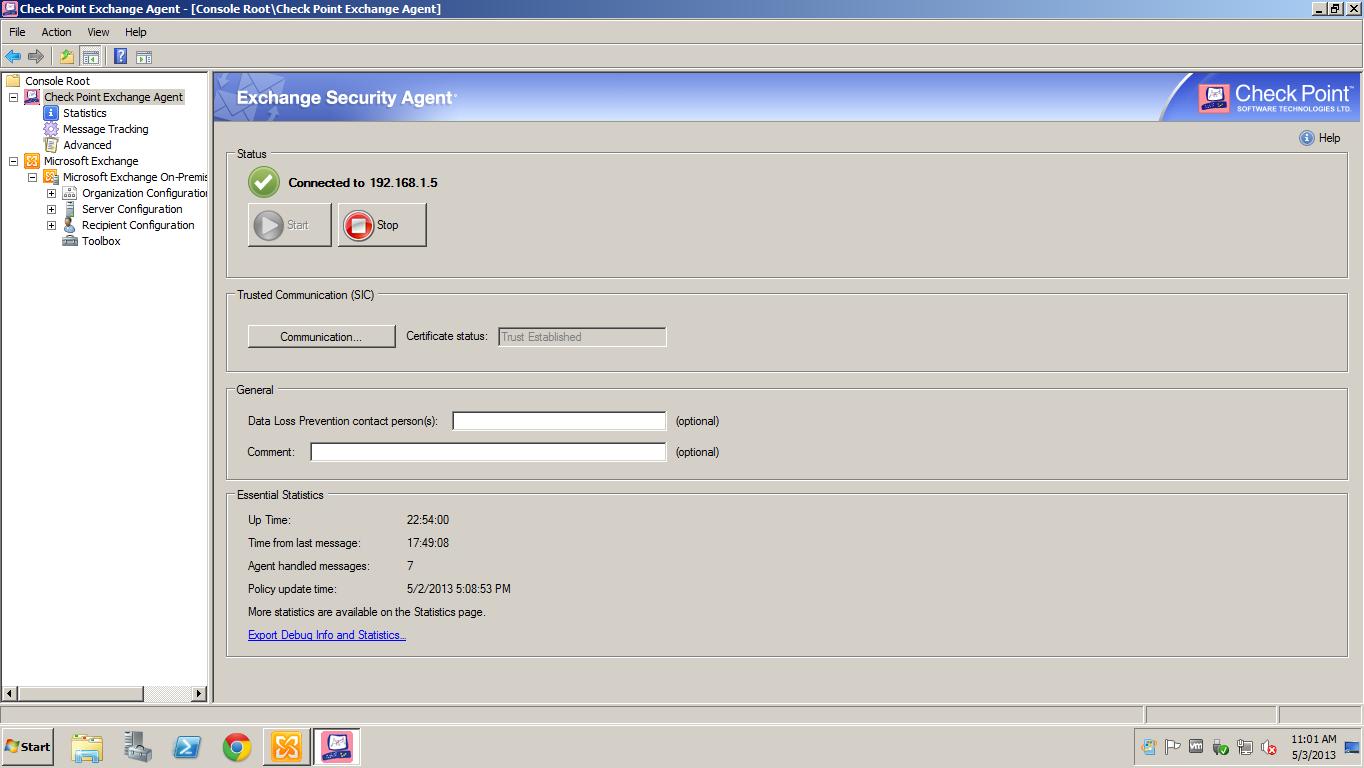
3.Once you have installed the the exchange agent on both exchange server as well as on dashboard you can initialize the sic between the gateway and the exchange agent.
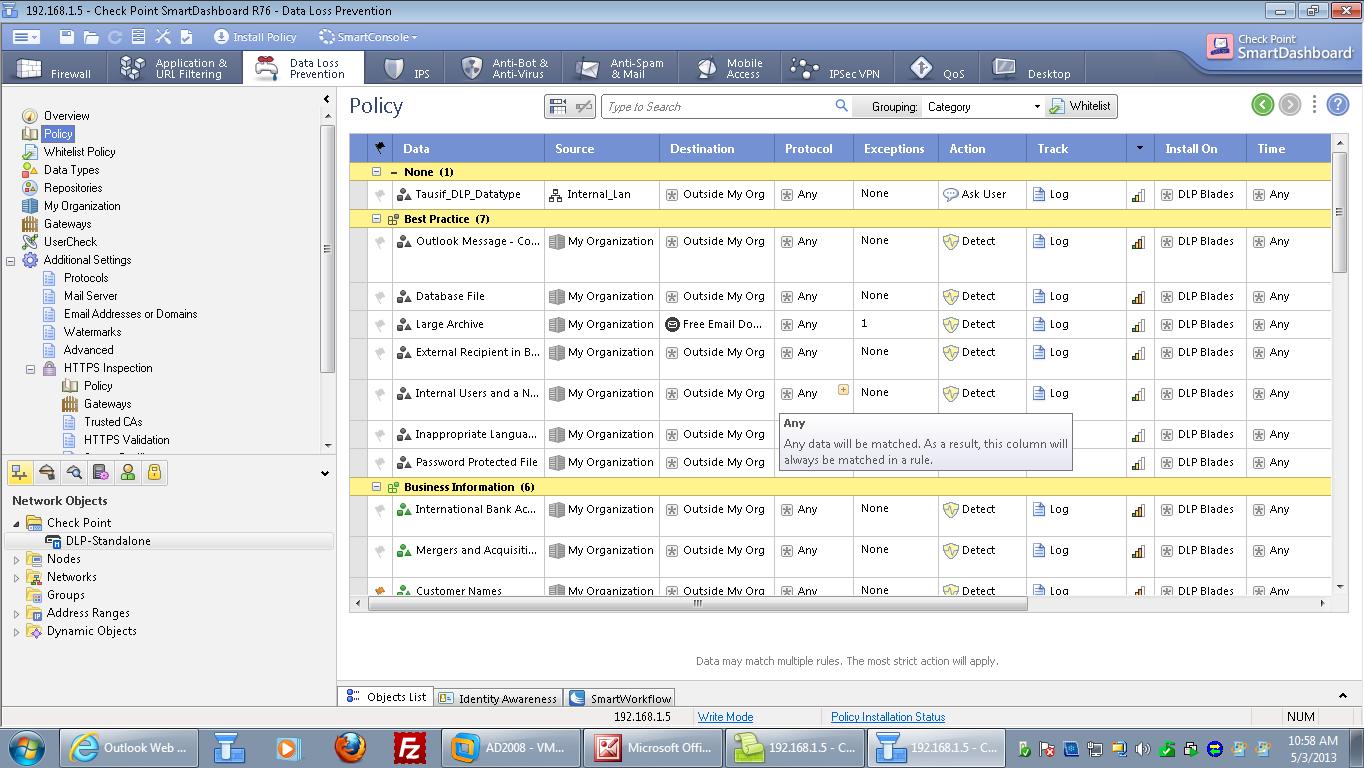
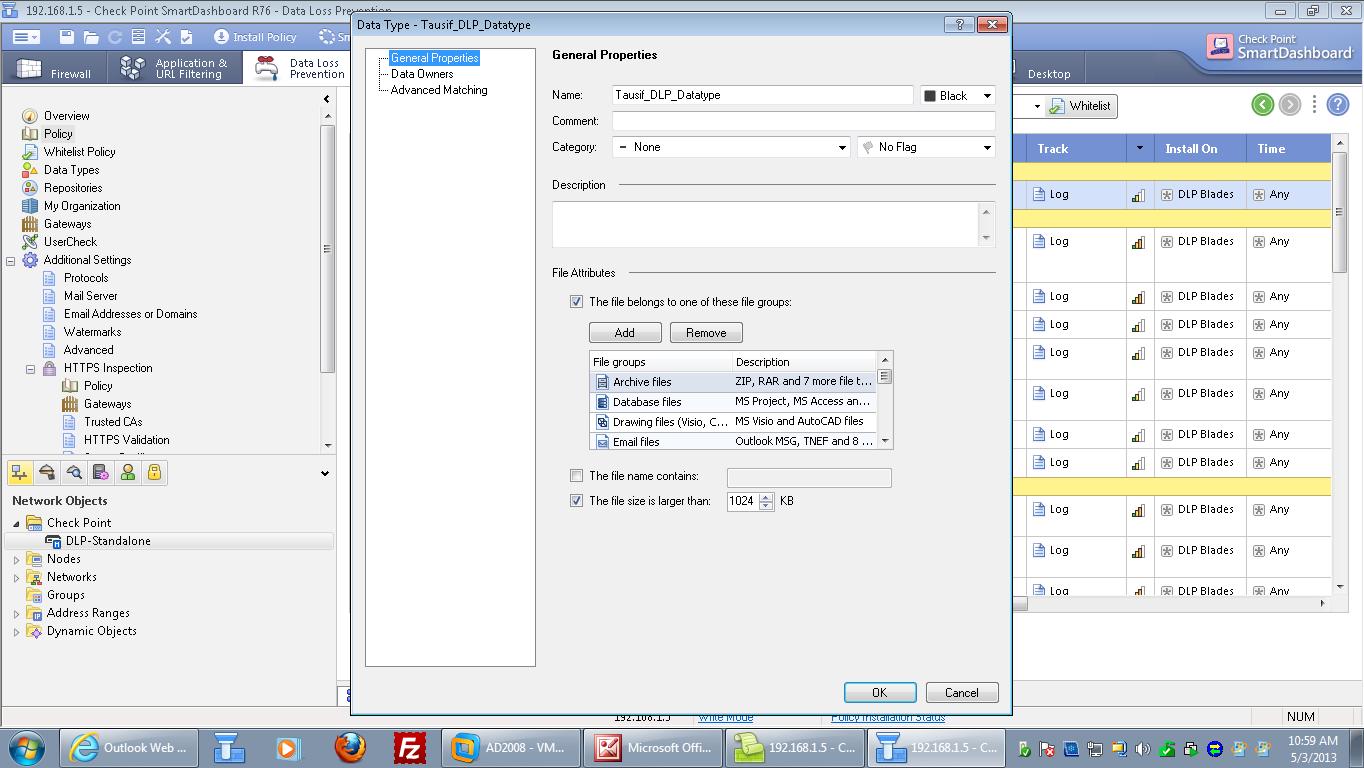
4.The
DLP rules remain the same, the dlp out of the box policy usually does
not work so you can create custom data types and use the same in the
rule base please refer to the screen shots below.
5.Also for dlp to work optimum you need to edit a parameter under $DLPDIR/dlp/config/dlp.conf, you need to edit the consider_ip_address_in_smtp to yes refer to screen shot below.
6.Once the dlp agent is installed and configured you can see the following stats on the dlp agent.







Comments
Post a Comment