How to Install Gaia on an IP Appliance
Youtube Click HERE
Youtube Click HERE
How to Install Gaia on an IP Appliance
Objective:
Clean installation of Gaia on an IP Appliance with IPSO
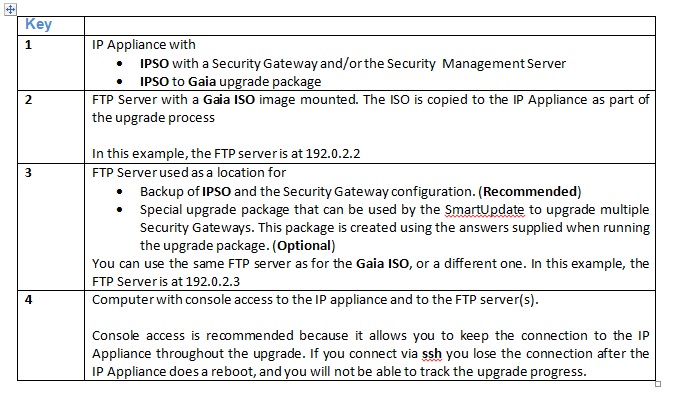
Set up the environment:
Procedure:
Step 1: Get the IPSO to Gaia boot-manager package and the Gaia ISO image.
https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doShowupgradewizard
Step 2: Point the Gaia ISO on an FTP server:
Method:
- Using Isomorphic tool transfer the image file and make pen drive bootable.
- Then transfer the contents of same pen drive to the pc where ftp server is configured. Extract it and place it in a folder (here the folder name is GAIA).]
- After extraction, you have to run the *.bat file.
Open
up a command prompt, a black screen comes up. Drag and drop your .bat
file onto the window. If that doesn’t work us cd (change directory) to
go to where the file is and then press enter. I'll give you an example,
let’s say execute.bat is on my desktop:
start>run>cmd (enter) then with the window open cd C:\GAIA/(enter) then execute.bat (enter).
start>run>cmd (enter) then with the window open cd C:\GAIA/(enter) then execute.bat (enter).
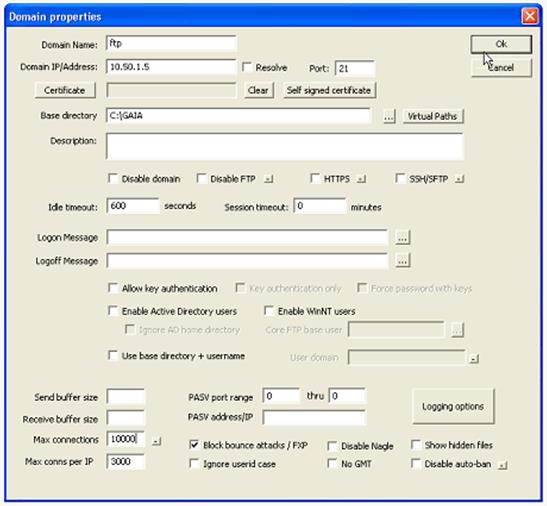
- Check for the FTP server configuration parameters and point the ISO folder path (here my path is C:/GAIA) to be installed.
Initially:
- Parameters to be set are
Step3: Now download the R7X.XX Gaia boot manager (*.sh) and place it in the appliance location /script. Give chmod 777 and Install as shown below.
- Verify that the boot manager is located in the logical drive ad0 by running the command
ipsctl –a | grep CF
The output will be similar to
hw:disk:ad:0:location = InternalCF
hw:disk:ad:0:type = CF-INTERNAL-IDE
Once the Gaia boot manager is installed successfully, appliance will reboots and (press 1) shows as below.
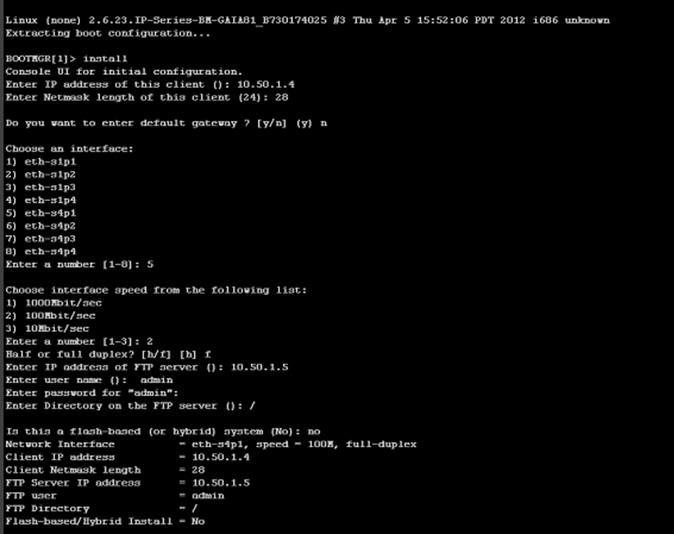
Step4:
Follow the instructions and enter the data. Make sure Ftp server
interface is up and running (here interface from appliance to ftp is
eth-s4p1).
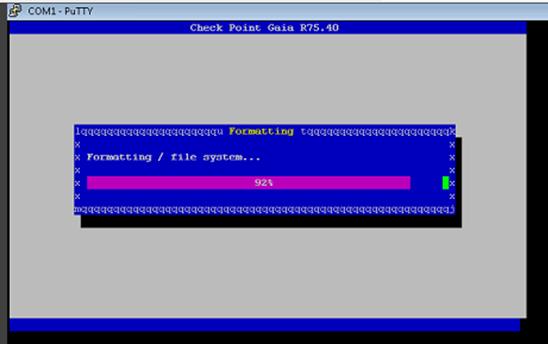
Device reboots and starts installing Gaia if all the values are correct
- System restarts once the installation is completed.
Step5: Now we can run first time wizard by using the IP address of the appliance











Comments
Post a Comment